SeCore, state-of-the-art quantitative optimal security assurance made available
- Standard agnostic evaluation
- Quantitative and qualitative metrics
- Optimal mitigation

State-of-the-art methodology and tool for confidence in product security
SeCore is a benchmark score tool for software and hardware. The methodology includes the processes, activities, and algorithms for improving the conduct of security evaluation and assessment. Pilots have been tested so far in the healthcare domain.
More about SeCoreWHAT WE OFFER
Customer Benefits
SeCore’s methodology includes the process, activities, and algorithms for how to improve conducting security evaluation and assessments.
OUR SOLUTION
Features
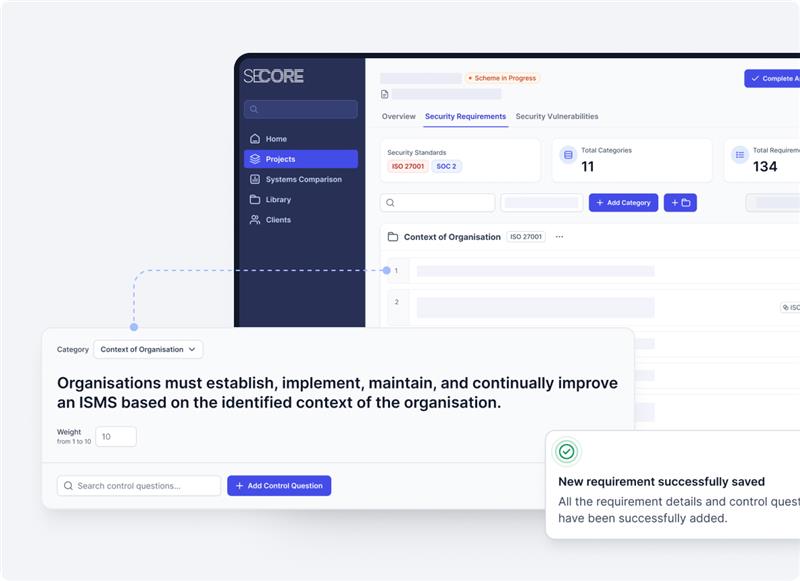
Library Support
Easy and fast setup with a built-in library covering most relevant security frameworks, standards, and guidelines.
Design
User-friendly design and interactive dashboard to present and interact with a comprehensive set of quantitative assurance metrics.
AI-Assisted Assurance
Integrate AI at different steps in the security assurance process.
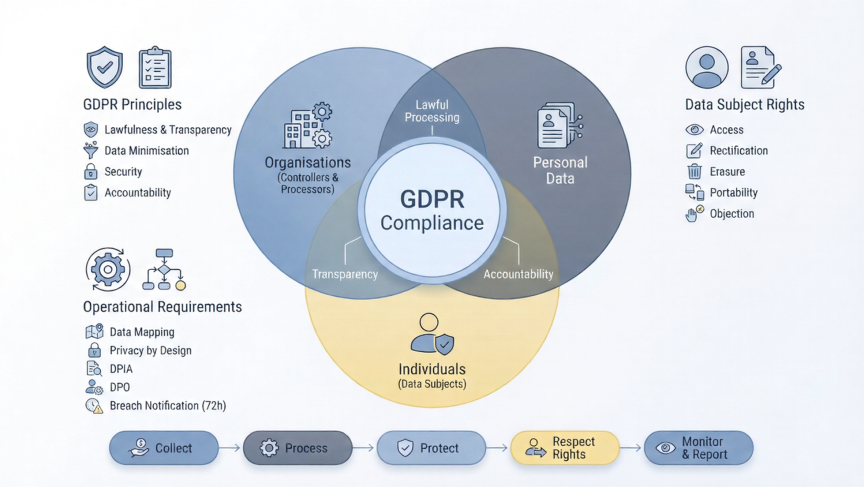
Security Compliance Made Available
Evaluate and assess multiple standards simultaneously through one evaluation process.
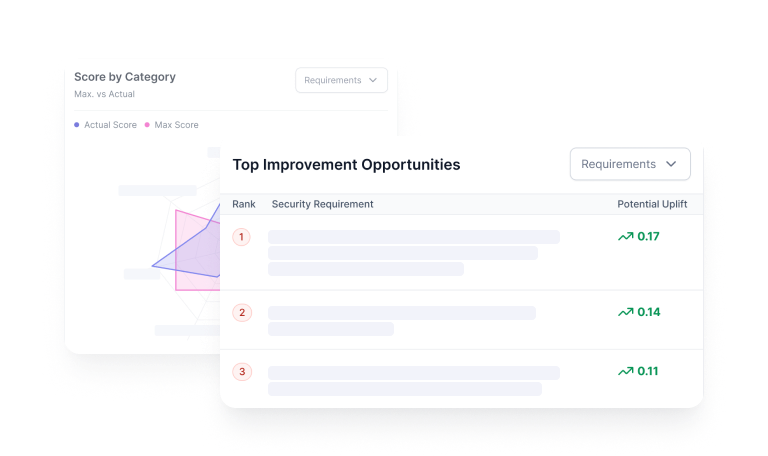
Benchmark
Compare the security levels among various IT/OT systems of the same type, or track the security level of one system over time.
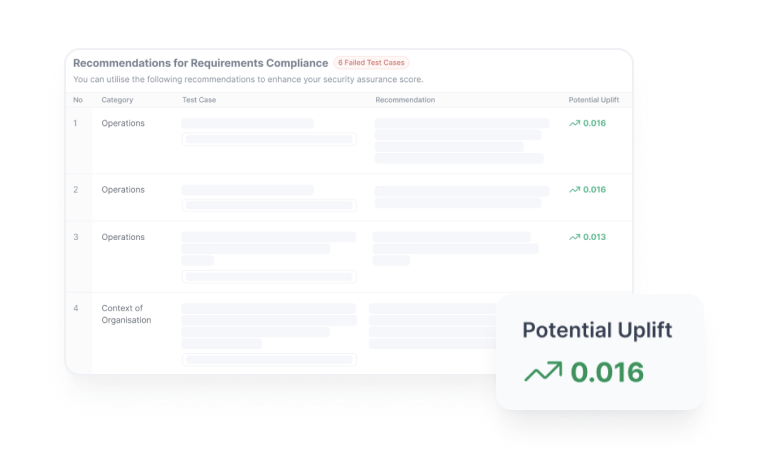
Optimal Plan
List different mitigation plans and recommend the most optimal and cost-efficient plan that maximises the security improvement level with the least possible cost.
WHAT WE DO
Our Services
Security Assurance: A Structured Approach
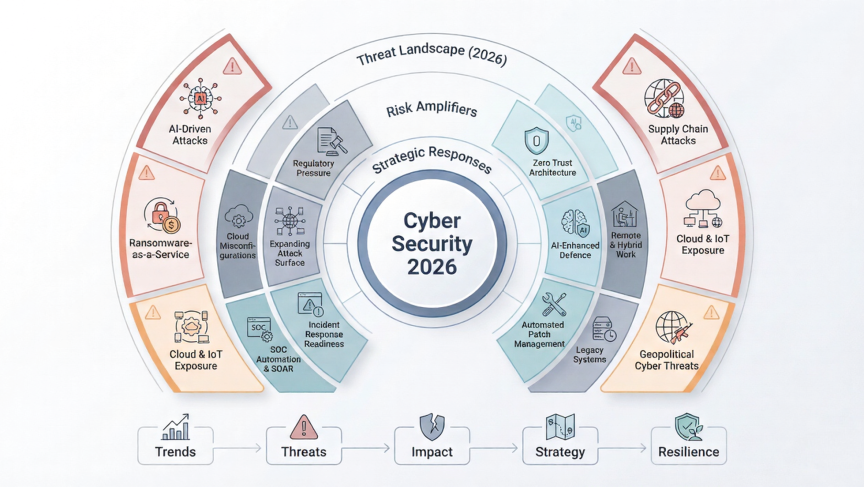
The process is designed to provide a comprehensive and measurable assessment of a system's security posture, moving beyond traditional subjective evaluations to deliver actionable insights. Secore provides the framework as well as tools and knowledge to enhance the security levels of IT/OT systems. This is particularly relevant in today's complex digital landscape, where continuous evaluation and risk-informed decision-making are paramount.
Security Assurance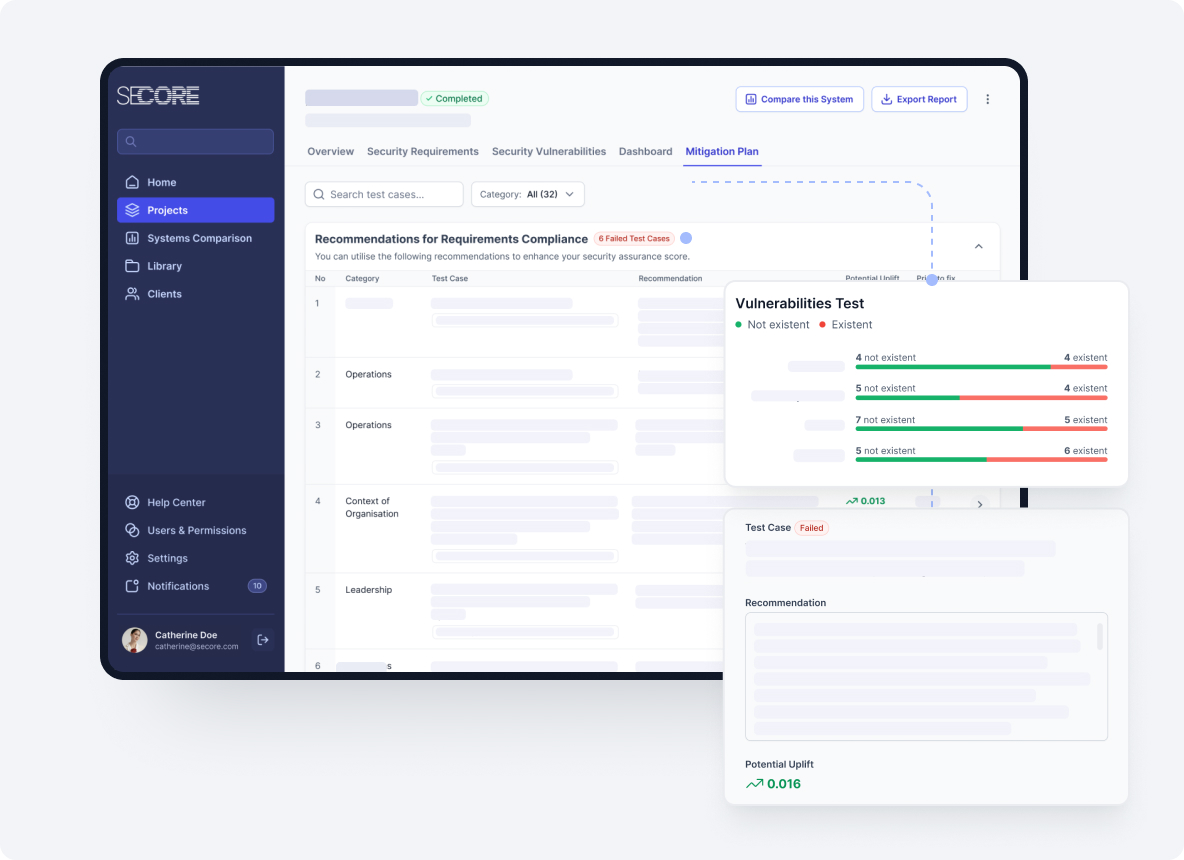
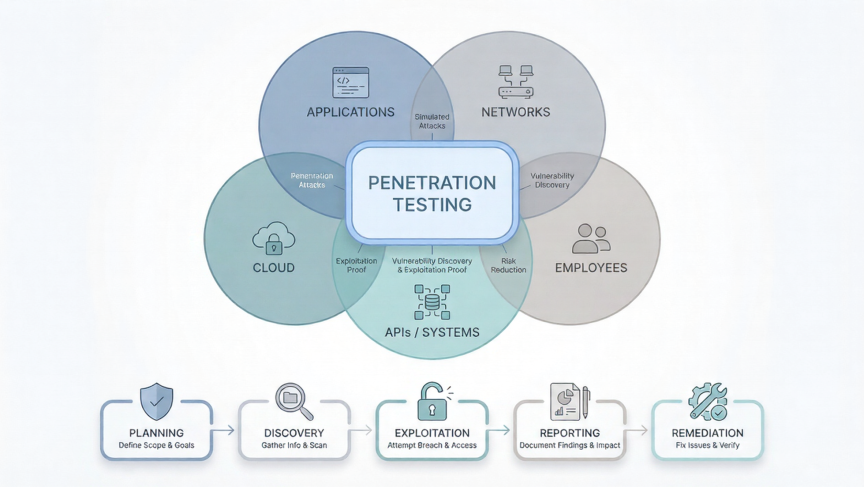
Penetration Testing – Identify & Mitigate Cybersecurity Risks
SeCore delivers certified penetration testing designed to identify and fix security vulnerabilities before cybercriminals can exploit them. Our team uses advanced techniques to simulate real-world cyberattacks, providing you with the insights and solutions you need to protect your digital assets.
Penetration TestingLATEST
Publications
We are highly impressed with the comprehensive approach and rigorous analytical framework provided by SeCore in the realm of quantitative security assurance. Their expertise has enabled us to accurately quantify our security risks, identify vulnerabilities, and implement targeted mitigation strategies. The clarity and precision of their assessments have significantly enhanced our confidence in our security posture, ensuring that our critical assets are well-protected. We highly recommend their services to any organization seeking data-driven, measurable security solutions.
Nasma Jizawi
Owner, Interteller LTD

Partnering with SeCore for our security assurance needs has been a transformative experience. Their comprehensive quantitative approach provided us with precise, data-driven insights into our security posture, enabling us to identify vulnerabilities that were previously overlooked. The transparency and professionalism demonstrated throughout the engagement instilled a strong sense of confidence in our security strategy. Thanks to their expertise, we have significantly enhanced our risk management capabilities and are better equipped to protect our assets and stakeholders. We highly recommend their services to any organization seeking rigorous, measurable security assurance.
Klodian Murrja
Partner, Murrja & Partners Law and Consultancy

SeCore provided us with a level of clarity and structure in security assurance that we had not experienced before. Their quantitative assessments transformed vague concerns into measurable insights, enabling us to make informed, data-backed decisions. The process was smooth, professional, and transparent from start to finish. We now have a clear roadmap for strengthening our security posture. I would highly recommend Secore to any organization serious about aligning security investments with real, quantifiable risks.
Dr.Namir Shehade
CEO, leaders aesthetics medical center
Working with SeCore has been invaluable for our compliance journey. Their detailed, metrics-driven reports not only highlighted vulnerabilities but also mapped directly to regulatory requirements, saving us both time and resources. Their structured approach gave our management team confidence that our security strategy is both effective and defensible in front of auditors. I cannot recommend Secore enough for organizations facing complex compliance and regulatory challenges
Dr.Amir JamalAlddin
CEO, Beyond Group
LATEST
Blog
TRUSTED BY
Our Partners

![]()





Create your own fully controlled testing environment
Purchase a subscription plan for your company and conduct the assessment yourself.

Get an expert-led assessment implementation
Work directly with security experts who guide, validate and optimise every step of the assessment.